Introduction
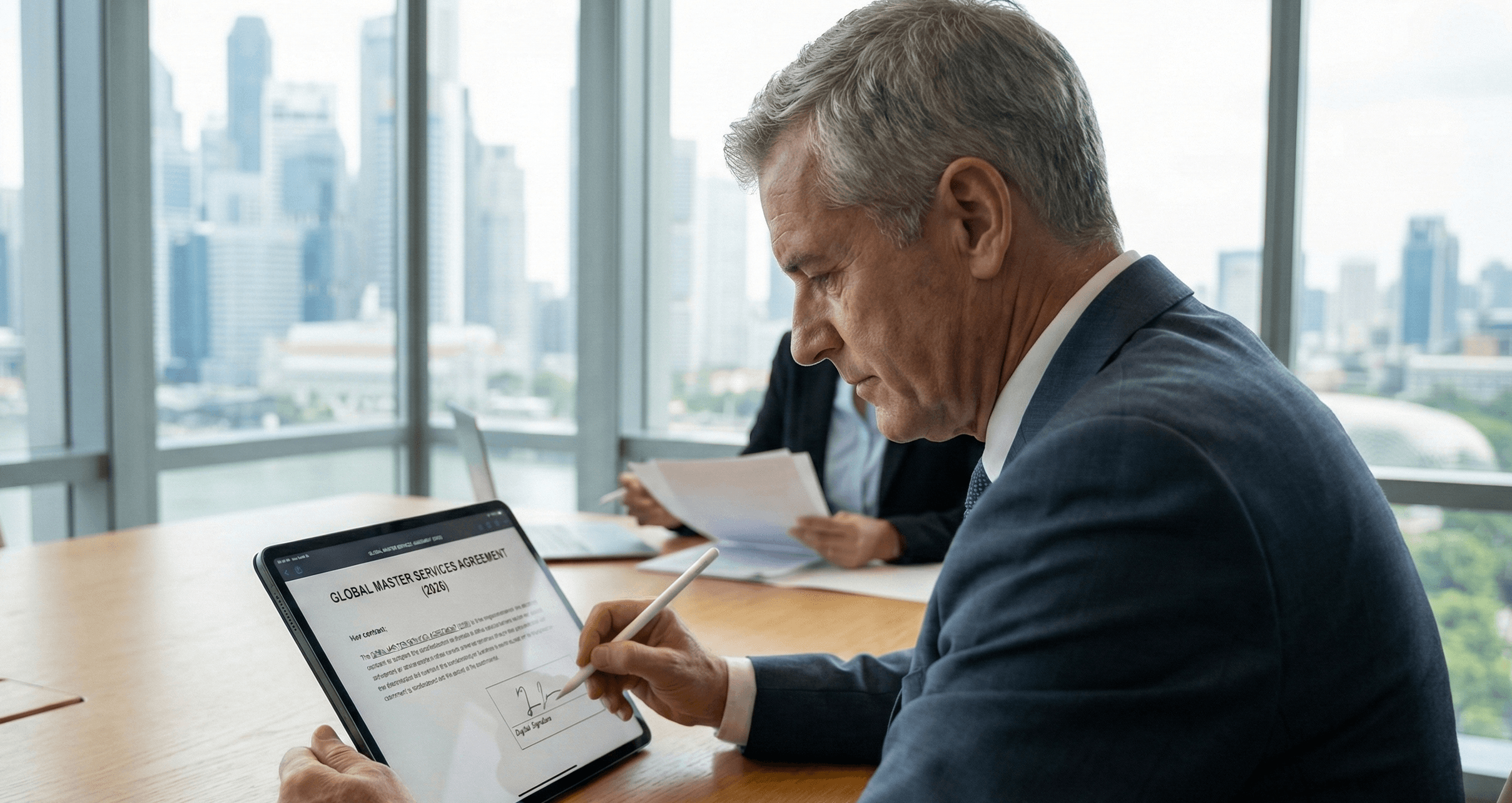
Stop using "electronic signature" and "digital signature" interchangeably. For legal and compliance leaders handling high-stakes international or FDA-regulated matters, confusing them is a serious risk.
The distinction is binary: An electronic signature is a legal concept capturing the intent to sign. A digital signature is a technical mechanism ensuring the document’s integrity. An electronic signature shows a user agreed. A digital signature proves the document hasn't changed since they agreed.
For routine workflows, indicating intent to sign is sufficient. However, when closing critical deals, you must understand the key difference between a simple "click-to-sign" and a highly secure Qualified Electronic Signature (QES). Choosing wrongly could mean your contract is not legally binding. This guide strips away vendor marketing to help you choose the precise validation level your risk profile demands.
What Is an Electronic Signature?
Laws like the U.S. ESIGN Act define "electronic signature" broadly, establishing their baseline legal validity. It includes any electronic symbol, sound, or process used by a person to show they intend to sign a document.
The definition focuses entirely on consent, not security. It verifies that an action took place, but rarely validates the actor's identity or the document's integrity.
Types of electronic signatures often include these common business examples:
Click-wrap Agreements: Checking a box ("I accept these terms") within a software interface.
Email Approvals: Typing a name at the bottom of a formal email correspondence.
Basic Document Signing: Pasting a scanned image of a handwritten signature into a PDF or Word document.
The Limitation: While legally binding for many standard commercial transactions, simple electronic signatures lack technical armor. If a user types their name on a contract, there is often no cryptographic evidence preventing a third party from altering the clauses above the signature after the fact.
What is a Digital Signature?
What are digital signatures in a technical sense? They are not a separate legal category but a specific, high-security subset of electronic signatures.
It relies on Public Key Infrastructure (PKI) to link the identity of the signer to the document, ensuring robust validity and verification. When a digital signature is applied, the software does not merely place an image on the page. It generates a cryptographic "hash"—a unique string of characters derived from the document's contents.
Why This Matters for Security and Compliance:
Tamper Evidence: If a single character in the contract is modified after signing, the cryptographic hash breaks. The PDF viewer will immediately flag the signature as "Invalid."
Identity Link: The signature is linked to a unique digital certificate. This makes it very hard for a signer to later claim in court that they did not sign the document.
In essence, while an electronic signature records a decision, a digital signature secures the evidence, offering the primary benefits of digital signatures: trust and integrity.
Why You Need Certificate Authorities (CAs)
A digital signature is technically robust, but without a trusted third party to verify it, it holds little weight. You can create a digital ID yourself, but partners will not trust it. Technically, you can generate a digital ID locally, but external partners will not validate it. It lacks third-party verification, similar to a self-printed driver's license.
This is why Certificate Authorities (CAs) are essential for validity and verification. A CA is a organization that verifies your identity before issuing a digital certificate. When you sign a document using a CA-backed credential, the recipient isn't just trusting you; they are trusting the rigorous vetting process of the CA. This is the gold standard for how to get digital signatures that are globally accepted.
The Visual Indicator:
A valid CA certificate generates a green checkmark in PDF readers, verifying the document's integrity.
Conversely, signatures lacking CA verification trigger a "Signature Unknown" warning, alerting compliance teams to potential risks.
Comparing Digital Signature and Electronic Signature: Key Differences
When comparing digital signature and electronic signature, the distinction is clear: "Electronic Signature" is the umbrella term for the category, while "Digital Signature" is the specific technology. For decision-makers, the choice comes down to the balance between security requirements and user friction.
Types of Digital Signatures (SES, AES, and QES)
Global regulations (such as eIDAS) categorize signatures into three distinct levels. Choosing the correct tier is about balancing security and compliance with user experience.
| Type | Security Level | Identity Verification | Best Use Case |
|---|---|---|---|
| Simple (SES) | Basic | Minimal. Often just an email address; no real identity proof required. | Internal HR forms, holiday leave requests, low-risk approvals. |
| Advanced (AES) | Medium | Linked to the signer. Must be capable of identifying the user and detecting any changes. | Sales contracts, NDAs, standard B2B agreements. |
Implementation Strategy: Matching Risk to Workflow
The winning strategy to choose the right signing solution is to map your signing method to the asset’s value, ensuring you don't over-complicate simple tasks or under-secure critical assets.
High-Risk Scenarios: Use Cases for Digital Signatures (QES)
For Life Sciences (FDA 21 CFR Part 11), Cross-Border Legal Disputes, or IP Transfers, data integrity is non-negotiable.
The Rule: Mandate Qualified Electronic Signatures (QES).
The Critical Requirement: Ensure your solution generates a comprehensive Audit Trail. A signature might be legally binding on its face, but without a background log recording the timestamp, IP address, and identity verification method, it is not verifiable in court.
Low-Risk Scenarios: Go Electronic (SES)
For Internal HR forms, IT tickets, or Standard Procurement, speed is the priority.
The Rule: Use Simple Electronic Signatures (SES).
The Efficiency Check: Adding complex identity verification steps (like video calls) here creates unnecessary friction and kills adoption. Keep the workflow frictionless.
Best Practices for Signature: Avoid the "PDF Scan" Trap The most dangerous habit in modern business is printing a document, signing it with a pen, scanning it back to PDF, and emailing it.
Why it fails: This image is just pixels. It contains no metadata, no audit trail, and can be easily copy-pasted onto a fraudulent contract. It provides the illusion of security with none of the legal protection.
Conclusion
The debate between "electronic" and "digital" signatures isn't academic—it’s a risk management decision regarding the future of digital signature adoption in your firm.
If you treat every signature as a simple checkbox, you expose your organization to compliance gaps. If you treat every signature as a cryptographic ceremony, you paralyze your operations. In the complex landscape of global compliance, the goal is to balance security with agility.
NotaSign helps organizations streamline this balance, ensuring you have the valid evidence you need—whether for a quick internal approval or a critical cross-border contract—without the operational headache.
If your high-value agreements rely on simple pasted images, it is time to upgrade your security posture. 👉Contact the NotaSign Team